GitOps: Transforming Modern DevOps Workflows
Introduction
In the fast paced world of cloud native development, teams constantly look for ways to reduce manual steps, improve reliability and keep production environments in sync with code. Traditional DevOps practices rely on scripts, ad hoc processes and siloed tools which can lead to configuration drift and slow feedback loops. GitOps emerges as a disciplined approach that extends the principles of version control to the entire delivery pipeline, turning Git repositories into the single source of truth for both application code and infrastructure state.
Core Concept
At its core GitOps is the practice of defining the desired state of a system declaratively in Git and using automated agents to continuously reconcile the live environment to match that state. Any change to the system is made by submitting a pull request, which triggers validation, testing and automated deployment, ensuring that every modification is auditable, reversible and traceable.
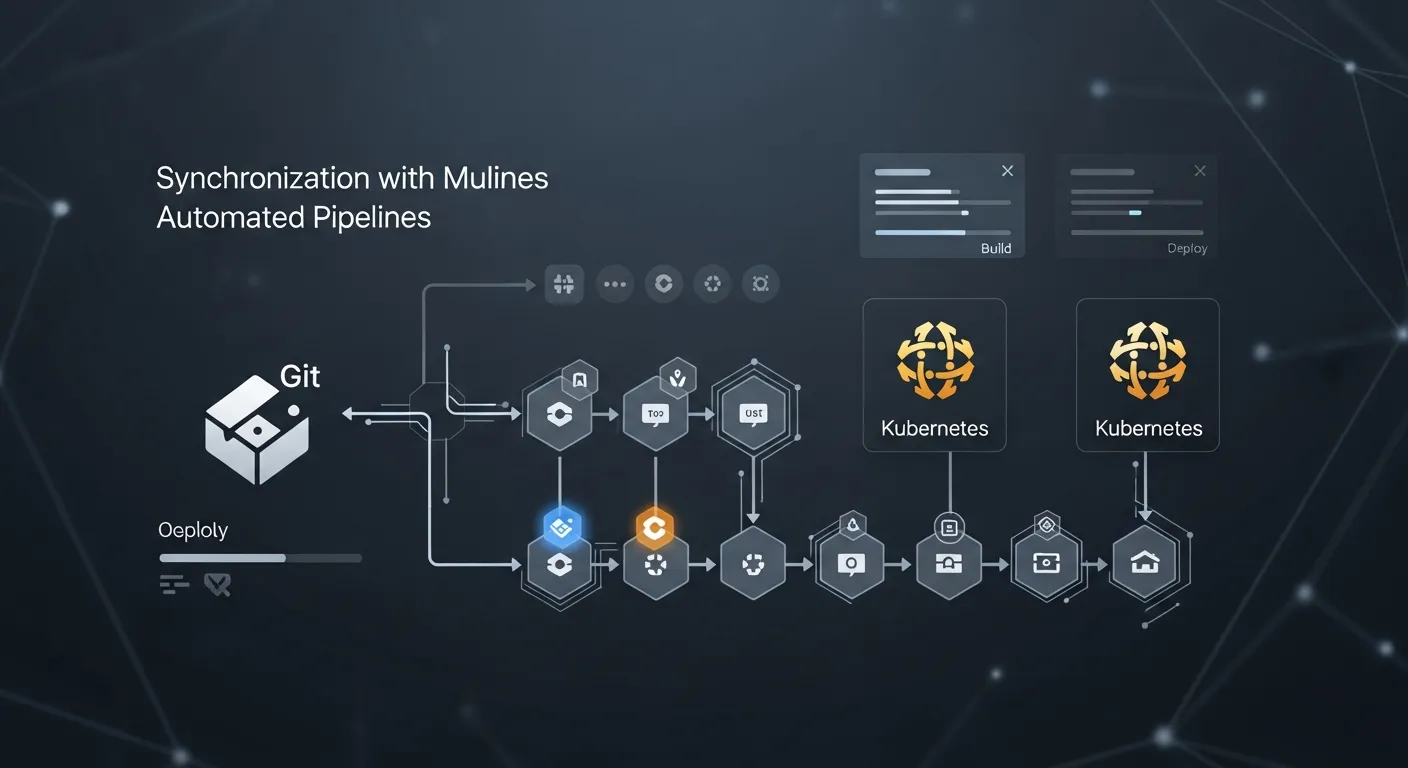
Architecture Overview
A typical GitOps architecture consists of a Git repository that stores declarative manifests, a continuous integration system that builds and validates changes, and a continuous deployment engine that watches the repository for updates. When a new commit appears, the deployment engine pulls the manifests, calculates the delta, and applies the necessary changes to the target platform, such as a Kubernetes cluster or cloud provider. Observability tools monitor the reconciliation process and surface drift or failures, while policy engines enforce compliance before changes are applied.
Key Components
- Git Repository as source of truth
- Declarative Manifests (YAML, JSON, HCL)
- Continuous Reconciliation Engine (Argo CD, Flux)
- CI Pipeline for testing and image building
- Policy Enforcement (OPA, Gatekeeper)
- Observability and Alerting
How It Works
Developers create a feature branch and modify declarative files to describe the new state. A pull request triggers the CI pipeline to lint, test and containerize the application. Once the PR is approved and merged, the GitOps controller detects the new commit, fetches the updated manifests and performs a diff against the live cluster. It then applies only the required changes using the platform's API. If the deployment succeeds, the system reports a healthy state; if drift is detected later, the controller automatically rolls back or re‑applies the desired configuration.
Use Cases
- Kubernetes cluster configuration management
- Multi‑environment promotion from dev to prod
- Infrastructure provisioning on cloud providers
- Edge device fleet updates
- Serverless function version control
Advantages
- Single source of truth eliminates configuration drift
- Full audit trail and easy rollback via Git history
- Automation reduces manual errors and speeds delivery
- Improved collaboration through pull request workflow
- Consistent deployments across multiple environments
Limitations
- Initial learning curve for declarative tooling
- Complexity when managing large monolithic manifests
- Potential latency due to reconciliation intervals
- Requires robust Git governance and access controls
Comparison
Traditional CI/CD pipelines often rely on imperative scripts that push changes directly to environments, making it hard to track the exact state over time. Configuration management tools like Ansible or Chef provide automation but lack a built in versioned source of truth for the entire system. GitOps combines the benefits of declarative configuration with Git's auditability, offering tighter feedback loops and safer rollbacks compared to these older approaches.
Performance Considerations
The reconciliation frequency of the GitOps controller directly impacts how quickly changes propagate; high frequency improves responsiveness but can increase API load on the target platform. Scaling the controller horizontally and using shallow clones of the repository help maintain performance in large organizations. Caching of manifests and incremental diff algorithms further reduce resource consumption.
Security Considerations
Security is anchored in signed Git commits, branch protection rules and role based access control for both the repository and the deployment engine. Secrets should never be stored in plain text; instead use secret management solutions integrated with the GitOps pipeline. Policy as code tools can enforce compliance checks before any change reaches production, and audit logs from Git and the controller provide traceability for incident investigations.
Future Trends
Looking beyond 2026 GitOps is expected to integrate deeper with AI driven drift detection, automatically suggesting corrective actions before failures occur. Extensions to serverless and edge computing will bring GitOps principles to function as a service platforms and IoT devices. Policy‑as‑code frameworks will become native components of the GitOps stack, enabling real time compliance enforcement across hybrid clouds. Additionally, low code interfaces will allow non‑technical stakeholders to propose changes via visual editors that generate the underlying declarative code.
Conclusion
GitOps reshapes modern DevOps by turning Git into the operational control plane, delivering faster, safer and more transparent deployments. While it introduces new tooling and governance requirements, the benefits of reduced drift, automated reconciliation and immutable audit trails make it a compelling foundation for cloud native organizations seeking to scale their delivery pipelines with confidence.
