Terraform Cloud vs Self-Hosted: Choosing the Right IaC Platform
Introduction
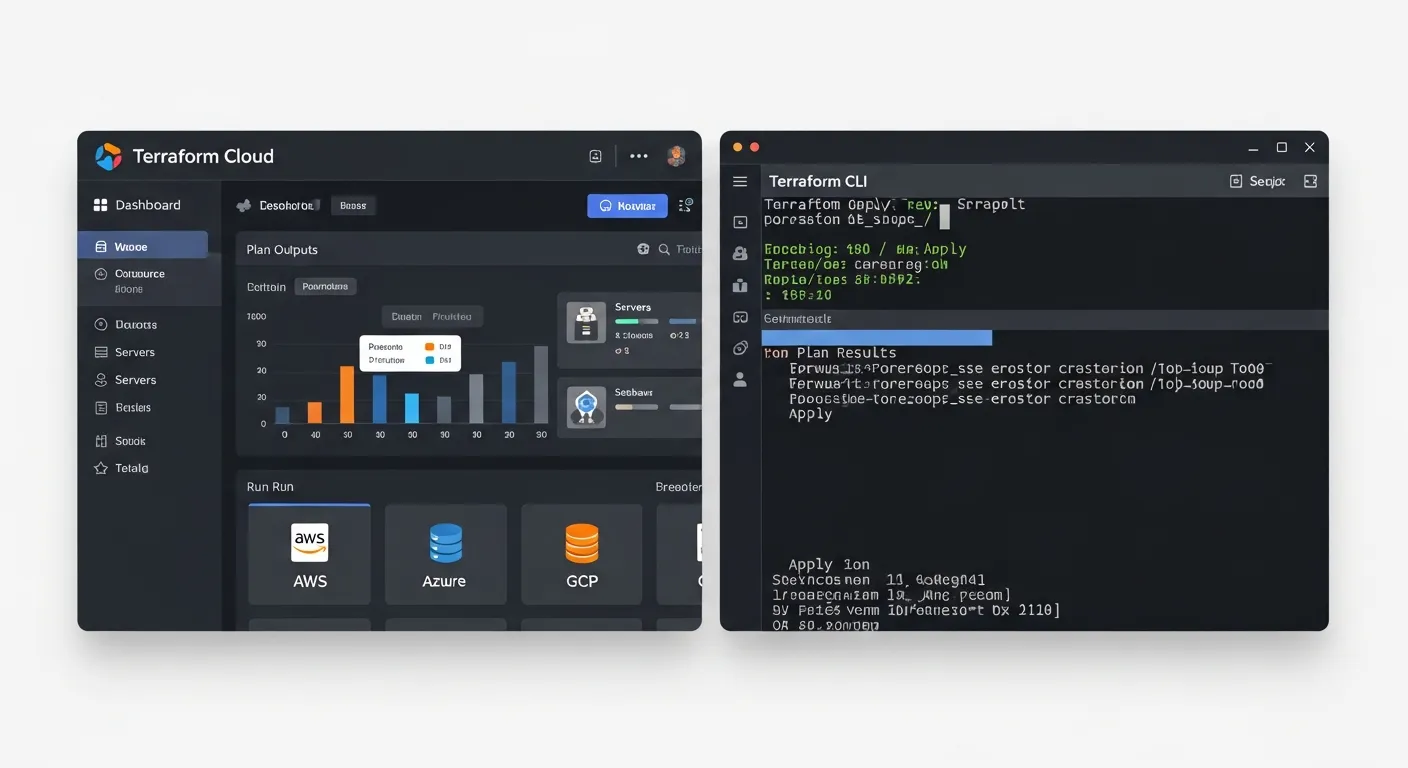
Infrastructure as code has become a cornerstone of modern DevOps, and Terraform leads the market with its provider ecosystem and declarative language. As organizations scale, the decision between Terraform Cloud, a managed SaaS offering, and a self-hosted deployment of Terraform Enterprise becomes critical. This article unpacks the core differences, architectural patterns, and practical scenarios that guide the choice.
Core Concept
At its core, Terraform separates the planning and execution phases from the state storage. Terraform Cloud bundles these responsibilities into a hosted service that adds collaboration, governance, and run automation. A self-hosted installation replicates the same capabilities on premises, giving teams full control over data residency, network topology, and integration points.
Architecture Overview
Terraform Cloud runs on a multi‑tenant cloud platform with shared services for state storage, remote runs, policy enforcement, and VCS integration. Users interact through the web UI, CLI, or API. A self‑hosted deployment consists of Terraform Enterprise components installed on customer infrastructure: a web server, a database for state, a private network for workers, and optional add‑ons such as Sentinel policy service. Both models rely on the Terraform CLI for local development but differ in where the remote operations occur.
Key Components
- Terraform CLI
- Terraform Cloud workspace
- State storage backend
- Run tasks and automation
- Version control system integration
- Policy as code engine
How It Works
When a user runs terraform plan locally, the configuration is sent to the remote backend. In Terraform Cloud the workspace receives the plan, executes it in an isolated run environment, and stores the resulting state in a managed S3‑compatible bucket. In a self‑hosted setup the same workflow occurs on customer‑managed worker nodes that pull the configuration from the VCS, run the plan, and write state to the internal database. After approval, terraform apply is triggered, and the changes are applied to the target cloud or on‑prem resources.
Use Cases
- Enterprise teams needing centralized governance and audit trails
- Startups preferring low‑maintenance SaaS with built‑in collaboration
- Regulated industries with strict data residency and compliance requirements
- Organizations with existing on‑prem infrastructure that must keep state isolated
Advantages
- Terraform Cloud offers instant onboarding, no infrastructure to manage, and built‑in VCS integration
- Self‑hosted provides full control over network, storage encryption, and compliance boundaries
- Both platforms support Sentinel policy as code for governance
- Remote runs eliminate local machine dependencies and ensure consistent execution environments
Limitations
- Terraform Cloud introduces recurring subscription costs and depends on internet connectivity
- Self‑hosted requires dedicated ops resources for installation, upgrades, and scaling
- Feature parity may lag for self‑hosted versions depending on licensing tier
- Network latency can affect remote run performance for distributed teams
Comparison
Compared with alternatives such as Pulumi SaaS or AWS CloudFormation, Terraform Cloud and self‑hosted Terraform share the advantage of provider agnosticism and a mature ecosystem. Pulumi adds a programming language layer but lacks the same level of policy enforcement out of the box. CloudFormation integrates tightly with AWS but cannot manage multi‑cloud resources. The choice therefore hinges on the breadth of environments and the need for a unified IaC tool.
Performance Considerations
Remote state storage introduces network round‑trips for each plan and apply. Terraform Cloud mitigates this with globally distributed data centers, while self‑hosted deployments can place the state database in the same data center as the workers to reduce latency. Concurrent runs are limited by workspace settings; scaling workers horizontally improves throughput for large teams. Caching of provider plugins and using lightweight execution containers further optimizes run time.
Security Considerations
Both models encrypt state at rest and in transit. Terraform Cloud provides managed key rotation and integrates with SSO providers for RBAC. Self‑hosted installations allow custom KMS solutions, private PKI, and isolation behind firewalls. Audit logging is available in both, but self‑hosted gives the ability to forward logs to on‑prem SIEM systems. Sentinel policies enforce compliance before any change reaches production, and secret management can be integrated via Vault or native provider mechanisms.
Future Trends
By 2026 the IaC market will see tighter integration with AI‑driven plan validation, deeper drift detection, and native support for immutable infrastructure pipelines. Terraform Cloud is expected to roll out real‑time collaboration features similar to document editing, while self‑hosted solutions will adopt container‑native orchestration for run workers, enabling auto‑scaling on Kubernetes clusters. Enhanced policy frameworks will incorporate risk scoring and automated remediation, making governance a proactive service rather than a manual checkpoint.
Conclusion
Choosing between Terraform Cloud and a self‑hosted deployment depends on organizational priorities. Teams that value speed, minimal ops overhead, and built‑in collaboration gravitate toward Terraform Cloud. Organizations with strict compliance, data residency, or custom integration needs benefit from a self‑hosted Terraform Enterprise installation. Understanding the architectural trade‑offs, performance impacts, and security controls ensures the selected model aligns with both current requirements and future growth.
