Terraform Cloud vs Self‑Hosted: Choosing the Right Deployment Model
Introduction
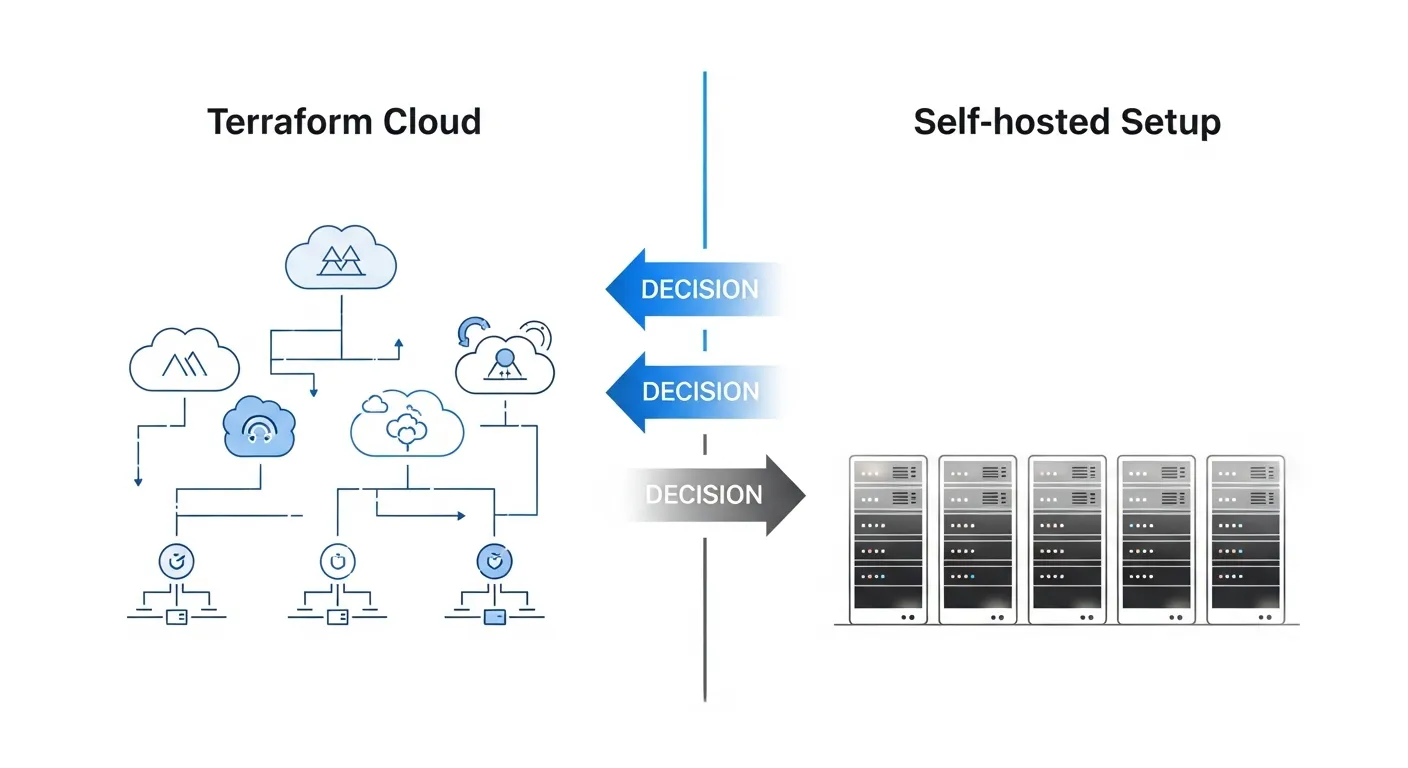
Terraform has become the de‑facto standard for infrastructure as code, but teams often wrestle with the decision to adopt the managed Terraform Cloud service or run a self‑hosted Terraform Enterprise instance. Both approaches deliver the same core provisioning engine, yet they differ dramatically in operational responsibilities, cost structures, and integration possibilities. This article walks through the key considerations, helping architects decide which model aligns with their technical, financial, and governance goals.
Core Concept
At its core, Terraform separates the declarative configuration language (HCL) from the execution engine. Terraform Cloud and Terraform Enterprise act as remote back‑ends that store state files, provide collaborative workflows, and enforce policy checks. The distinction lies in where the service runs: Terraform Cloud is a SaaS offering hosted by HashiCorp, while Terraform Enterprise is a self‑contained appliance that you install on your own infrastructure, whether on‑premises or in a private cloud.
Architecture Overview
In Terraform Cloud, users interact through a web UI, CLI, or VCS integration. HashiCorp manages the underlying compute, storage, and networking, offering built‑in high availability and automatic upgrades. Terraform Enterprise mirrors this architecture but places every component—API servers, workers, and the private registry—inside the customer’s control plane. This enables deep integration with internal authentication providers, custom networking, and compliance‑driven isolation.
Key Components
- Remote state storage
- Run queue and workers
- Policy as code (Sentinel)
- VCS integration
- Private module registry
- Audit logging and RBAC
How It Works
When a user runs terraform apply, the CLI uploads the plan to the remote backend. The backend queues the run, assigns it to a worker, and executes the plan against the target providers. Throughout execution, state files are read and written exclusively by the backend, eliminating local drift. After completion, the results—including logs, plan output, and policy violations—are stored and presented in the UI for review and approval. In a self‑hosted deployment, the same flow occurs, but the organization controls the worker fleet, storage backend (often PostgreSQL), and network egress, allowing tighter security controls.
Use Cases
- Startups and small teams seeking rapid onboarding with minimal ops overhead
- Enterprises with strict data residency, compliance, or custom authentication requirements
- Organizations needing deep integration with internal CI/CD pipelines and private registries
- Teams that require granular RBAC and audit trails for regulated environments
Advantages
- Terraform Cloud: zero‑maintenance infrastructure, automatic scaling, built‑in SSO, and predictable pricing tiers
- Terraform Enterprise: full control over data location, customizable networking, ability to run on air‑gapped environments, and integration with legacy identity systems
Limitations
- Terraform Cloud: limited to HashiCorp‑managed regions, less flexibility for custom compliance tooling, and reliance on external service uptime
- Terraform Enterprise: higher operational burden, need for capacity planning, and responsibility for patches, backups, and disaster recovery
Comparison
Compared with alternatives like Pulumi SaaS, AWS CloudFormation, or Ansible, Terraform’s strength lies in its provider ecosystem and declarative language. Terraform Cloud offers a managed experience similar to Pulumi SaaS, while self‑hosted Enterprise provides the on‑premise control that CloudFormation offers for AWS‑only stacks. The choice often hinges on multi‑cloud strategy versus vendor‑specific tooling.
Performance Considerations
Managed Terraform Cloud automatically scales workers based on concurrent runs, delivering consistent latency for most workloads. In self‑hosted setups, performance depends on the sizing of the worker pool, database tuning, and network topology. Organizations should monitor queue times, plan execution duration, and state file size, and provision additional workers or database replicas as needed to avoid bottlenecks during large-scale apply operations.
Security Considerations
Terraform Cloud encrypts state at rest and in transit, and supports SSO with SAML, OIDC, and LDAP. However, the shared nature of the SaaS platform may not meet strict regulatory mandates. Self‑hosted Enterprise enables end‑to‑end encryption, custom TLS certificates, and isolation within VPCs or on‑prem networks. Both models support Sentinel policy enforcement, but Enterprise allows custom policy pipelines that can integrate with internal compliance scanners.
Future Trends
Beyond 2026, HashiCorp is expanding Terraform Cloud with AI‑assisted plan reviews, tighter integration with GitOps workflows, and native support for confidential computing environments. Self‑hosted Enterprise will likely adopt a modular, container‑native architecture, enabling deployment on Kubernetes clusters and easier hybrid cloud management. Expect increased emphasis on policy as code, automated drift remediation, and tighter coupling with secret management platforms across both delivery models.
Conclusion
Choosing between Terraform Cloud and a self‑hosted Terraform Enterprise deployment is less about feature parity and more about operational philosophy. If your priority is speed, low overhead, and you trust a SaaS provider, Terraform Cloud delivers a frictionless experience. If you must keep state within controlled boundaries, need custom networking, or operate under strict compliance regimes, self‑hosted Enterprise provides the necessary control at the cost of added operational responsibility. Evaluate your organization’s risk tolerance, scalability needs, and long‑term cloud strategy to select the model that will sustain your infrastructure as code journey.
