Terraform vs Pulumi: Which IaC Tool Wins in 2026?
Introduction
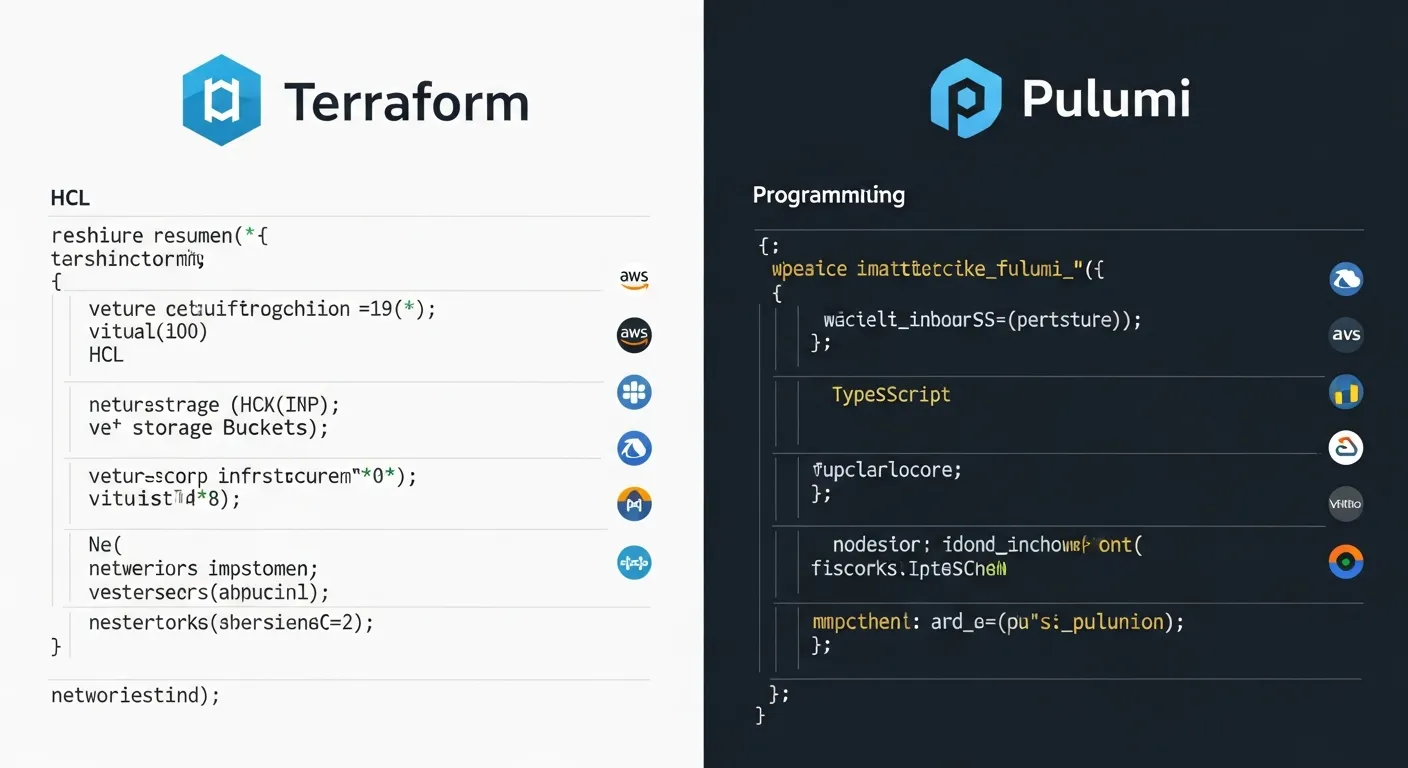
Infrastructure as Code (IaC) has become the backbone of modern cloud operations, allowing teams to version, test, and deploy infrastructure with the same rigor as application code. Two of the most popular IaC platforms today are Terraform, the open‑source champion from HashiCorp, and Pulumi, the newer entrant that lets developers write infrastructure using familiar programming languages. This article dissects their differences, helping architects choose the right tool for their 2026 cloud strategy.
Core Concept
At its core, IaC is about describing desired infrastructure state in a machine‑readable format and letting a tool reconcile that description with the real world. Terraform follows a declarative model where users define resources and let the engine compute the necessary actions. Pulumi blends declarative intent with imperative logic by allowing infrastructure to be expressed in general‑purpose languages such as TypeScript, Python, Go, or C#.
Architecture Overview
Terraform uses a provider‑plugin architecture. Each provider implements CRUD operations for a specific cloud or service, and the Terraform core orchestrates these plugins based on a dependency graph derived from HCL files. State is stored locally or remotely and acts as the single source of truth. Pulumi, by contrast, runs as a thin CLI that invokes language runtimes. User code compiles to a deployment graph, which Pulumi’s engine translates into cloud provider API calls. Pulumi stores state in its managed service or in self‑hosted backends, and it leverages the language’s type system for validation.
Key Components
- Terraform configuration files (HCL)
- Terraform state file
- Terraform providers
- Terraform CLI
- Pulumi programs (TypeScript, Python, Go, C#)
- Pulumi SDK
- Pulumi CLI
- Pulumi service backend
How It Works
Both tools start with a code authoring phase. In Terraform, users write .tf files, run terraform init to download providers, then terraform plan to see a preview of changes, followed by terraform apply to enact them. Pulumi users write code in their chosen language, run pulumi preview to view the diff, and pulumi up to apply. Terraform records resource IDs and metadata in a state file, while Pulumi records similar information in a stack file managed by the Pulumi service. During execution, each tool constructs a dependency graph, resolves ordering, and makes API calls to create, update, or delete resources.
Use Cases
- Provisioning multi‑cloud environments with a single language (Pulumi)
- Standardizing infrastructure across teams using HCL modules (Terraform)
- Embedding complex logic or loops in infrastructure definitions (Pulumi)
- Integrating with existing CI/CD pipelines that expect declarative plans (Terraform)
- Managing state in a highly regulated environment with remote backends (Terraform)
- Leveraging existing software engineering skill sets for infrastructure (Pulumi)
Advantages
- Terraform has a massive provider ecosystem covering virtually every cloud service.
- Terraform’s declarative HCL is easy for ops teams to read and review.
- Pulumi lets developers reuse existing libraries, unit tests, and IDE features.
- Pulumi supports true imperative constructs, making complex scenarios simpler.
- Both tools offer remote state backends and policy‑as‑code integrations.
Limitations
- Terraform’s HCL lacks the full expressive power of a programming language, leading to workarounds for loops and conditionals.
- Pulumi’s reliance on language runtimes can increase build times and requires developers to manage package dependencies.
- Terraform state management can become a bottleneck in large organizations if not properly segmented.
- Pulumi’s managed service introduces a dependency on external SaaS for state and secrets unless self‑hosted.
Comparison
Terraform excels in pure declarative workflows, broad provider support, and a mature ecosystem of modules and community tooling. Pulumi shines when teams want to apply software engineering practices—unit testing, type checking, and reuse of existing code—to infrastructure. In terms of learning curve, Terraform’s HCL is shallow for ops engineers, while Pulumi may require deeper programming knowledge. Cost considerations also differ: Terraform is free and open source with optional paid enterprise features, whereas Pulumi offers a free tier but charges for advanced collaboration and state management services.
Performance Considerations
Terraform’s plan phase can be slower for very large configurations because it must read the entire state and compute a full diff. Incremental planning and targeted applies mitigate this. Pulumi’s preview phase leverages the language runtime, which can be faster for code that already compiles, but large dependency graphs still incur overhead. Both tools support parallel resource creation, but Terraform’s explicit depends_on and Pulumi’s automatic graph analysis affect concurrency. Choosing a remote state backend with high‑throughput storage (e.g., S3 with DynamoDB locking) improves Terraform performance, while Pulumi’s managed service provides built‑in scaling.
Security Considerations
Secret management is critical. Terraform recommends using external secret stores (Vault, AWS Secrets Manager) and avoids committing sensitive values in state. Pulumi integrates with secret backends and can encrypt stack outputs automatically. Both platforms support policy‑as‑code: Terraform Sentinel for enterprise users and Pulumi Policy as Code using familiar languages. Auditing is easier with Terraform’s immutable plan files, whereas Pulumi’s programmatic approach requires careful code review to prevent accidental credential exposure.
Future Trends
Looking beyond 2026, IaC tools are converging with AI‑driven code generation, enabling auto‑completion of resource definitions based on natural language prompts. Terraform is expanding its CDK for Terraform (CDKTF) to support familiar languages, narrowing the gap with Pulumi. Pulumi is investing in tighter integration with serverless and edge computing platforms, and its ecosystem is adding first‑class support for GitOps workflows. Both tools will likely adopt more granular policy enforcement tied to supply‑chain security standards such as SLSA, and they will provide deeper observability through native tracing of infrastructure changes.
Conclusion
Choosing between Terraform and Pulumi hinges on team composition, existing skill sets, and the complexity of the infrastructure you need to manage. Terraform offers unmatched provider breadth and a straightforward declarative model ideal for ops‑centric teams. Pulumi empowers developers to treat infrastructure as code with the full power of modern programming languages, reducing boilerplate for complex logic. By understanding their architectural differences, performance profiles, and security features, architects can align the right IaC tool with their 2026 cloud roadmap and drive faster, safer deployments.
