Zero Trust Architecture: Secure the Modern Enterprise
Introduction
In today’s threat landscape enterprises can no longer rely on perimeter defenses alone. The rise of remote work, cloud services and sophisticated attackers demands a model that treats every request as untrusted. Zero Trust Architecture offers a comprehensive framework that shifts security focus from locations to identities, devices and data.
Core Concept
Zero Trust is built on the principle of never trust, always verify. It assumes that attackers may already be inside the network and therefore requires continuous authentication, authorization and encryption for every access attempt regardless of source.
Architecture Overview
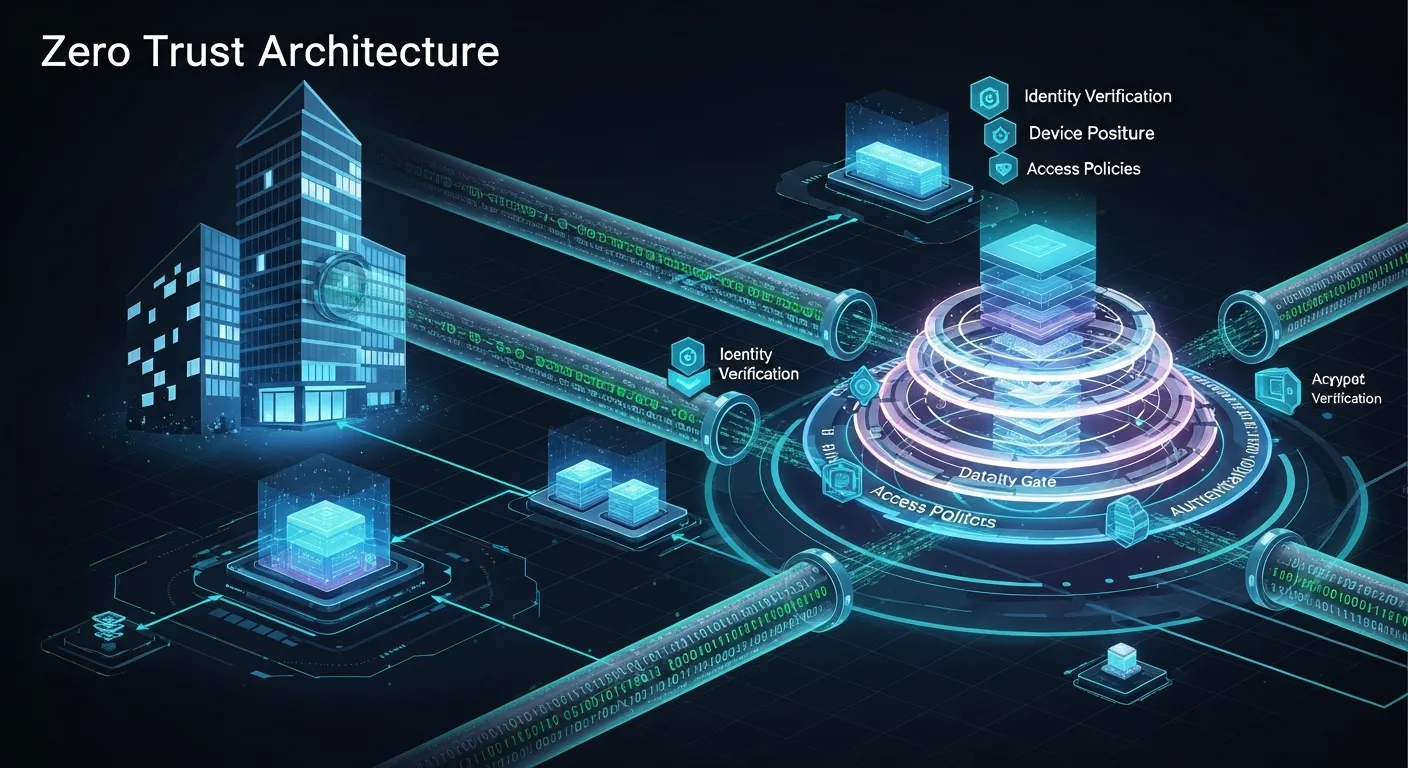
A Zero Trust design consists of a layered set of controls that span identity management, device health, network segmentation, application security and data protection. These layers work together to enforce least‑privilege access and to limit the blast radius of any breach.
Key Components
- Identity and Access Management
- Device Posture Assessment
- Micro‑segmentation
- Secure Application Access
- Data Encryption and Loss Prevention
How It Works
When a user or device requests a resource, the Zero Trust engine evaluates identity credentials, device compliance status, location, and behavior analytics. Based on policy rules it issues a short‑lived token that grants the minimal required permissions. All traffic is encrypted and inspected, and any deviation from expected patterns triggers adaptive controls such as step‑up authentication or session termination.
Use Cases
- Protecting remote workforce access to corporate SaaS applications
- Securing multi‑cloud environments with consistent policy enforcement
- Mitigating insider threats by restricting lateral movement within data centers
Advantages
- Reduces risk of breach propagation through strict least‑privilege policies
- Improves visibility and auditability of all access events
- Enables flexible support for hybrid and multi‑cloud architectures
Limitations
- Complexity of policy definition and management across diverse environments
- Potential performance impact if not optimized for high‑throughput workloads
Comparison
Compared with traditional perimeter security Zero Trust eliminates reliance on static firewalls and VPNs. Unlike basic MFA it adds continuous risk assessment and network segmentation, providing deeper protection than single‑factor approaches.
Performance Considerations
Implementing Zero Trust requires careful planning of authentication latency, token lifespan and traffic inspection points. Edge caching, distributed policy decision points and hardware acceleration can help maintain user experience while enforcing strict controls.
Security Considerations
Zero Trust must be coupled with robust identity governance, regular device posture updates and comprehensive logging. Failure to keep policies current can create blind spots that attackers could exploit.
Future Trends
By 2026 Zero Trust will integrate AI‑driven risk scoring, automated policy orchestration across edge and 5G networks, and deeper integration with confidential computing platforms to protect data in use.
Conclusion
Zero Trust Architecture is no longer a buzzword but a practical necessity for modern enterprises. By continuously verifying every interaction and limiting access to the smallest possible scope, organizations can build resilient defenses that adapt to evolving threats while supporting the flexibility of cloud and remote work.
